While towing vessels and operators may not have as wide an exposure to cyber attacks as other sectors of the maritime industry, it’s still a major threat in today’s environment. Unfortunately, it’s a threat that many companies are not addressing properly, according to industry experts.
“I would say the vast majority of operators are not prepared,” said Dean Shoultz, chief technology officer and founder of MarineCFO, a provider of software solutions for the industry. “Most of the big guys, say 30 or 40 boats or higher (are prepared), but the average 10- to 15-boat operator is not prepared at all.”
Towing vessel operators may believe that their exposure is less since their vessels, in many cases, are less sophisticated electronically than bluewater vessels. “There’s a lot less equipment that is digital or automated,” Shoultz said. But the risk is growing every day, and companies need to take steps to be prepared.
To help the towing industry, the American Waterways Operators (AWO) has come up with a list of best practices for cyber-risk management. Version 1.0 of the guide, prepared in partnership with the U.S. Coast Guard, is available here.
“What you are hearing about cyber issues can be highly technical and there can be a lot of jargon,” said Caitlyn Stewart, the AWO’s director of regulatory affairs. “It is sometimes the case that people think ‘There is no way I will be able to ever meet this challenge, since I don’t have the expertise.’”
AWO member companies “are incredibly diverse in size and complexity, and the safeguards necessary to protect one company’s cyber systems against attack and disruption may not be practicable for another’s,” the guidelines state. To ensure that cyber risk is reduced companywide, operators should incorporate the guidelines into their safety management systems.
The process involves looking at a company’s entire computer system to identify all access points to the system, from vessels to shoreside computers and devices. “The access points are where these vulnerabilities exist,” Stewart said. “The better handle a company has on those access points, the better it is going to be prepared and defend against a cyber incident.”
Once the risks are identified, the impact of an attack should be assessed. Then, the likelihood of an incident should be identified and assigned a risk probability ranging from “rare” to “almost certain.” The impact of that attack should then be assessed on a scale from minimal to severe. Specific procedures should be created with emphasis on how electronic systems can be protected and recovered in the case of an attack.
 |
|
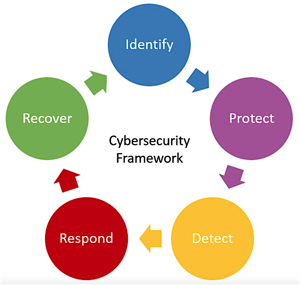
The Coast Guard has adopted the National Institute of Standards and Technology (NIST) Cybersecurity Framework for the service’s maritime industry guidance. At the core are five continuous functions: Identify physical and software assets, people, data and risks; protect assets by training users and mitigating risk; detect cyber incidents; respond with defined processes; and recover assets or systems affected by cyber incidents. |
|
Courtesy AWO |
Stewart does not believe that a major cyber attack has occurred in the towing industry. However, the global shipping company Maersk was the victim of a widespread attack in 2017. The attackers used a ransomware note that targeted Microsoft Windows systems, threatening to inflict losses of up to $300 million due to “serious business interruption.” Maersk was forced to reinstall 4,000 servers and 45,000 personal computers as a result.
In addition to their own electronic and computer systems, towing companies need to confirm that any work done by shipyards is secure. Shoultz said that when something changes during a construction, dry-docking or repowering project, operators should speak to the vendors working on their behalf. “They need to say, ‘Hey, explain to me what you are doing to ensure that I am OK,’” he said.
Another area of risk is any program that updates existing technology on a vessel. “Most of these modern engines and generators and propulsion systems have sensors that are reporting back to shore, or at least logging data points … and some vendors have the ability to reach in and remotely update the firmware,” Shoultz said.
AIS or GPS spoofing attacks also can directly impact vessel control. “If your navigation system goes down, or something like that, or if a radar device goes down, then you’re dead in the water,” Shoultz said.
Matt Real, information technology director at Devall Towing & Boat Service of Sulphur, La., said his company is in the beginning stages of addressing cybersecurity risks. Devall, which has 300 employees and operates 35 towboats, recently had company officials attend a session on cyber risk held by the Coast Guard.
Real said one of the main goals is to make sure employees are aware of the risk of phishing campaigns. “We have seen a large increase in email attacks,” he said. To help minimize the risk, each vessel runs cellphones, laptops and computer systems on a single stand-alone network, with the aim of reducing the impact of a cyber attack on those specific systems.
Shoultz said one of his clients recently dealt with a potentially serious cyber attack. A hacker got into the company’s network and impersonated the chief financial officer, took over the CFO’s email account and asked for a large sum of money to be sent.
“(The attack) failed because the purchasing agent said, ‘Hey, this isn’t like him, he would never do that,’” Shoultz said. “She walked down the hall and asked him, ‘Did you really just ask me to do this?’”

