It’s well known that computer hackers can breach ship navigation and operating systems with devastating results, but one security testing firm is noting another avenue of attack with potential for catastrophic harm: manipulating a vessel’s loading data.
Buckingham, England-based Pen Test Partners has focused on bulk carriers to illustrate this threat because one of its colleagues worked aboard a bulker and knows the risks of these ships breaking apart firsthand, said company partner and security expert Ken Munro.
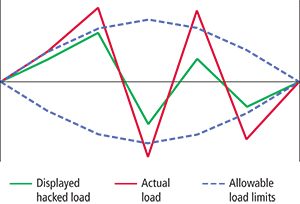
By remotely gaining access to a bulk carrier’s hull stress monitoring system (HSMS) — which ensures the even loading of cargo — hackers could deliberately cause an imbalance and strain a ship enough to sink it, Munro explained. Further, he said, once they’re in the system, hackers “can cause incorrect data to display” and deactivate alarms that would alert the crew to a problem.
The hackers’ aim could be to cause chaos, destruction and financial ruin, but sometimes it’s simpler than that, Munro said.
“Yes, it can be commercial motivation, that Shipping Line A would benefit from Line B being down, or ‘if you don’t pay us money, we’ll bring down your ship.’ Or they’re trying to stop critical cargo, like natural gas, from getting to where it’s needed,” he said. “But the thing is that hackers don’t always need motivation. People will do it because they can. They’ll play with something because it’s interesting, and they’re not really understanding the consequences.”
Pen Test Partners said ship operators must better understand what they can do to ensure their vessels can’t be hacked. That can come down to the most basic of steps, including making sure administrative passwords are changed frequently, that the latest software is installed and that a ship’s critical systems are segregated, Munro said.
 |
|
Courtesy Pen Test Partners/Pat Rossi illustration |
“It’s things like making sure a crewmember with a laptop doesn’t have access to your navigation and propulsion system, or someone doesn’t inadvertently bring malware aboard that could lead to your vessel being compromised,” he said.
Munro added that the maritime industry is 10 to 15 years behind other industries like financial services when it comes to cybersecurity, and that must change as hackers move on to new and less obvious frontiers.
Munro cited online resources that can be helpful for crewmembers and vessel owners, including a global initiative, www.becyberawareatsea.com, which offers a wealth of free information. Pen Test Partners has lots of free advice on its site as well and willingly shares it.
“At the moment, ship hacking is relatively rare,” he said. “And we are trying to share good practices before hackers take over.”
Sean Kline, director of maritime affairs for the Chamber of Shipping of America, agreed that raising awareness is key to keeping hackers at bay.
He said the threat to HSMS, especially on bulk carriers, is real, but it is just one of “millions of different ways cyberattacks can cause catastrophic results to the maritime industry.”
“It’s good to raise awareness of all of them,” Kline said. “All these things can happen. It’s all possible. So companies need to focus on blocking their windows and closing their doors to critical areas.”
Kline also agreed that the industry has to work more together, instead of everyone dealing with security matters individually. Toward that end, he noted, the International Chamber of Shipping has issued guidelines for cybersecurity on ships and continues to work to stay ahead of cyberthreats.

